How-To Guides about Computers & Programming

how to
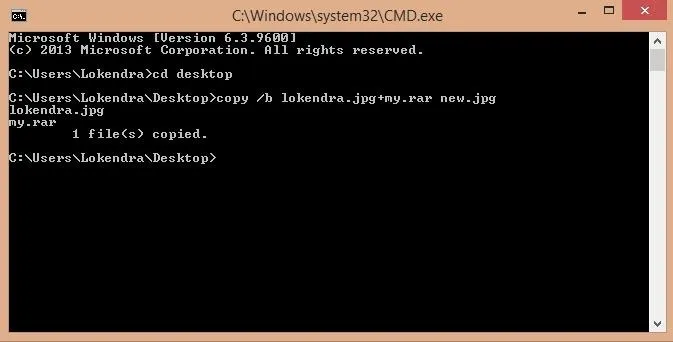
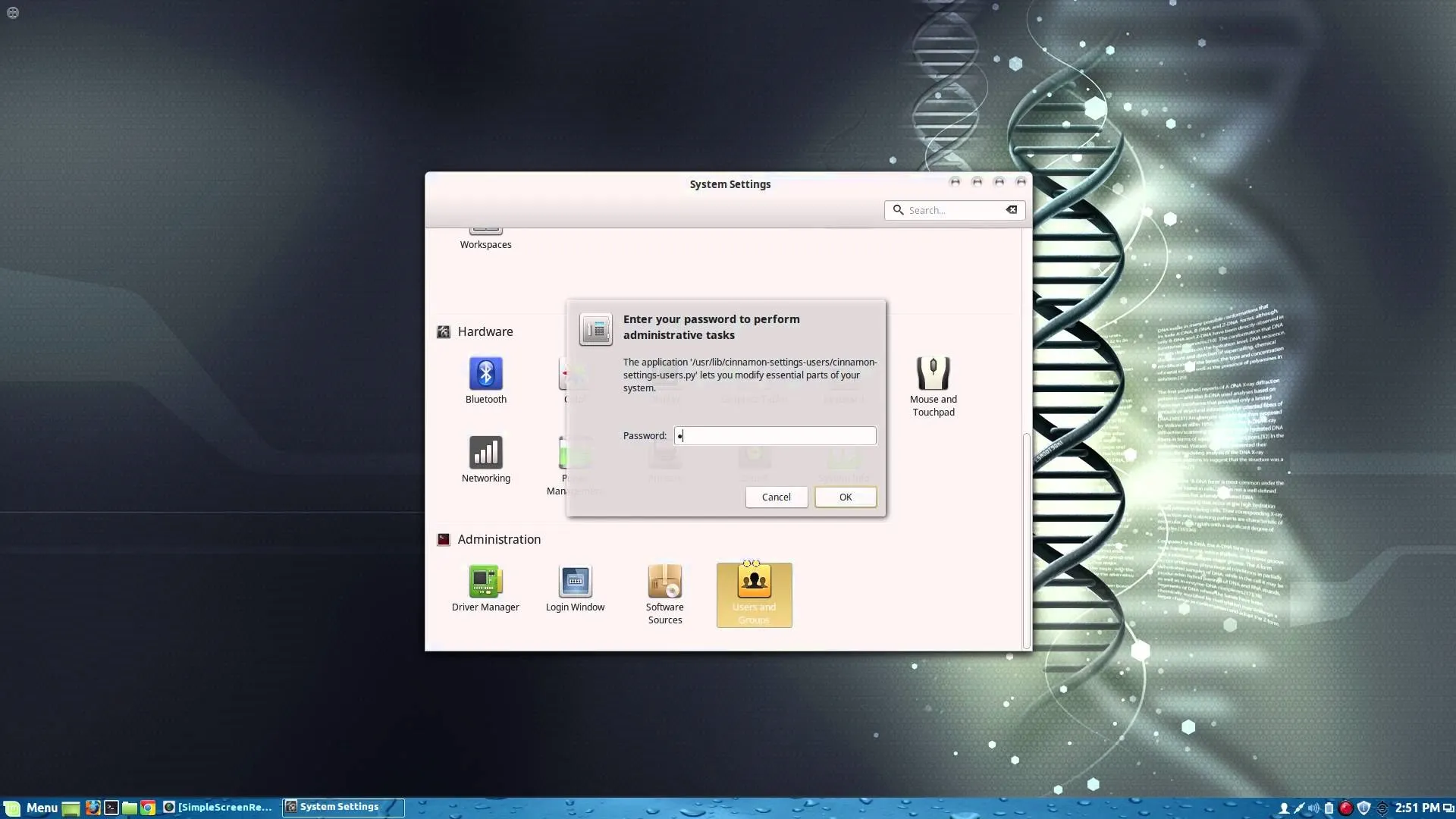
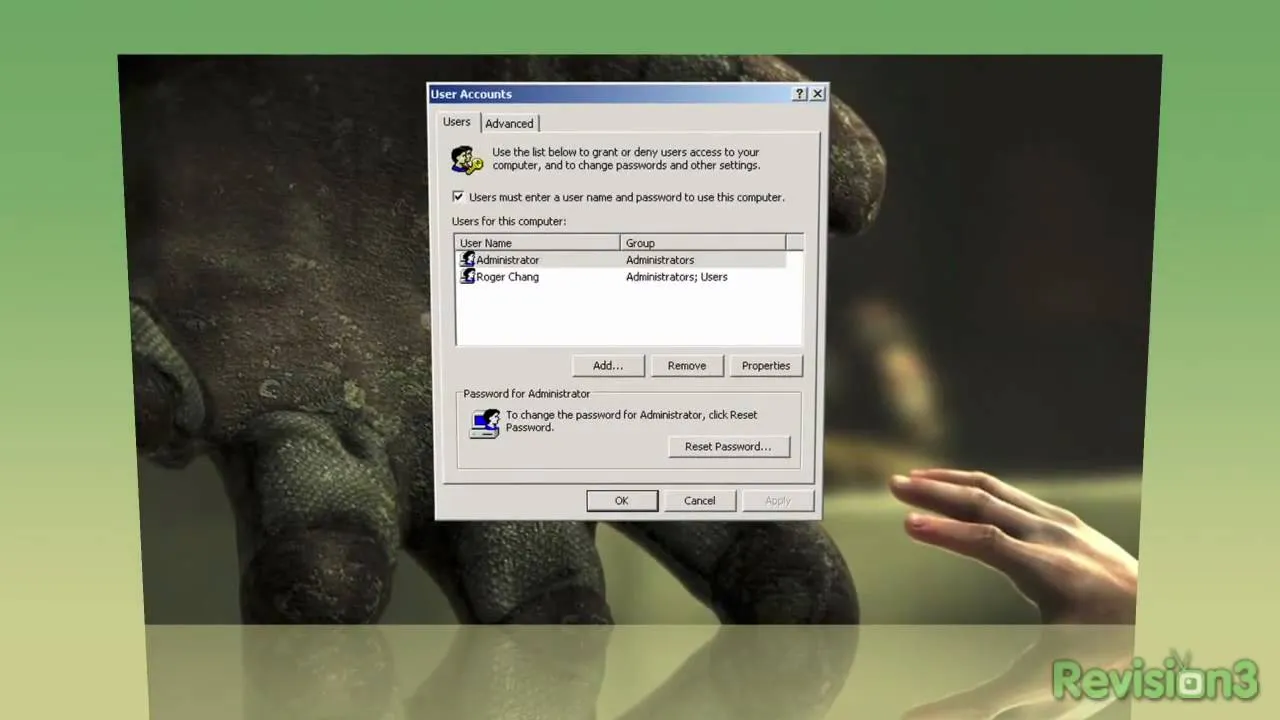
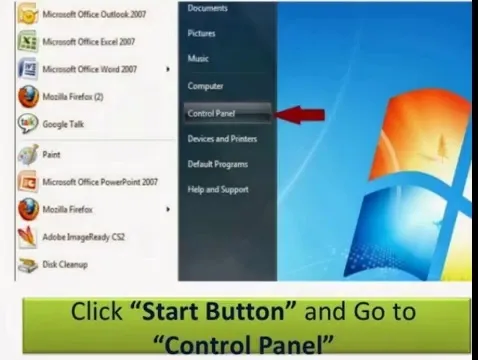
How to Create an Admin User Account Using CMD Prompt (Windows)

how to
How Long Would It Take to Crack Your Password?

how to
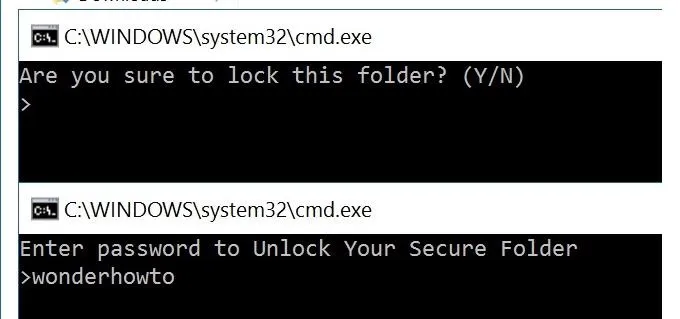
How to Lock Folder Without Any Software with Password






















Featured On WonderHowTo:
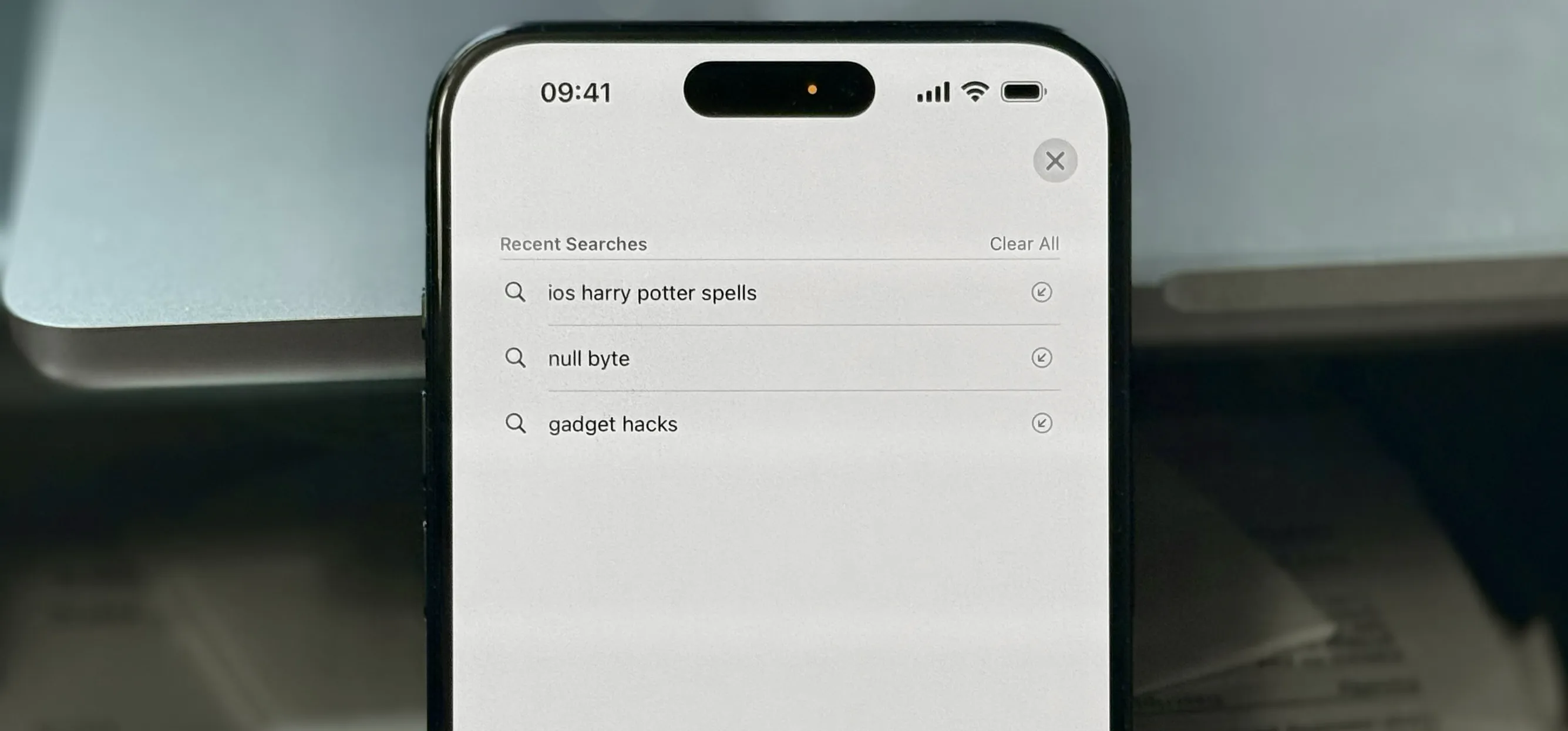
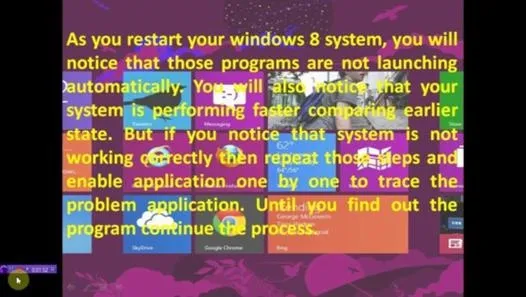
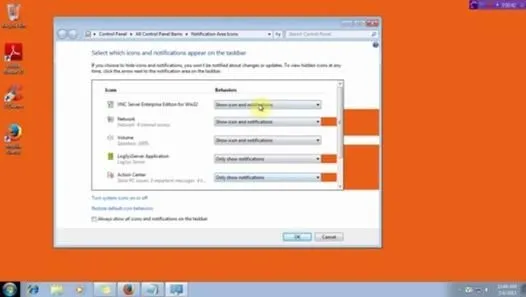
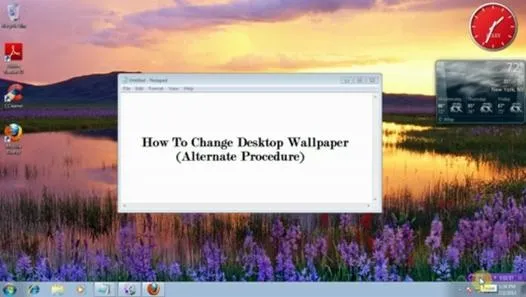
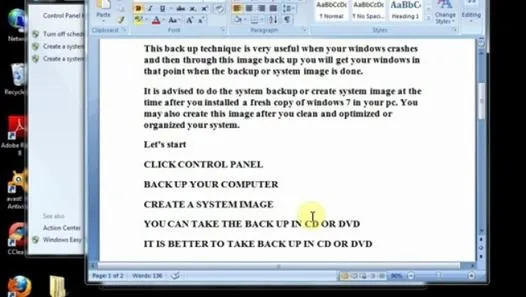
Productivity & Shortcuts







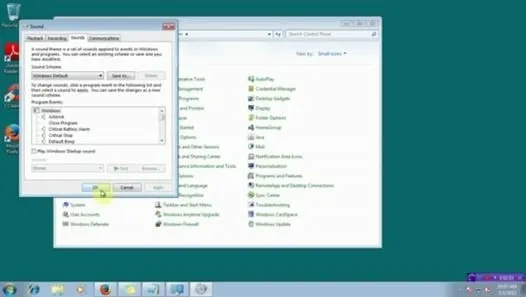
Featured On WonderHowTo:
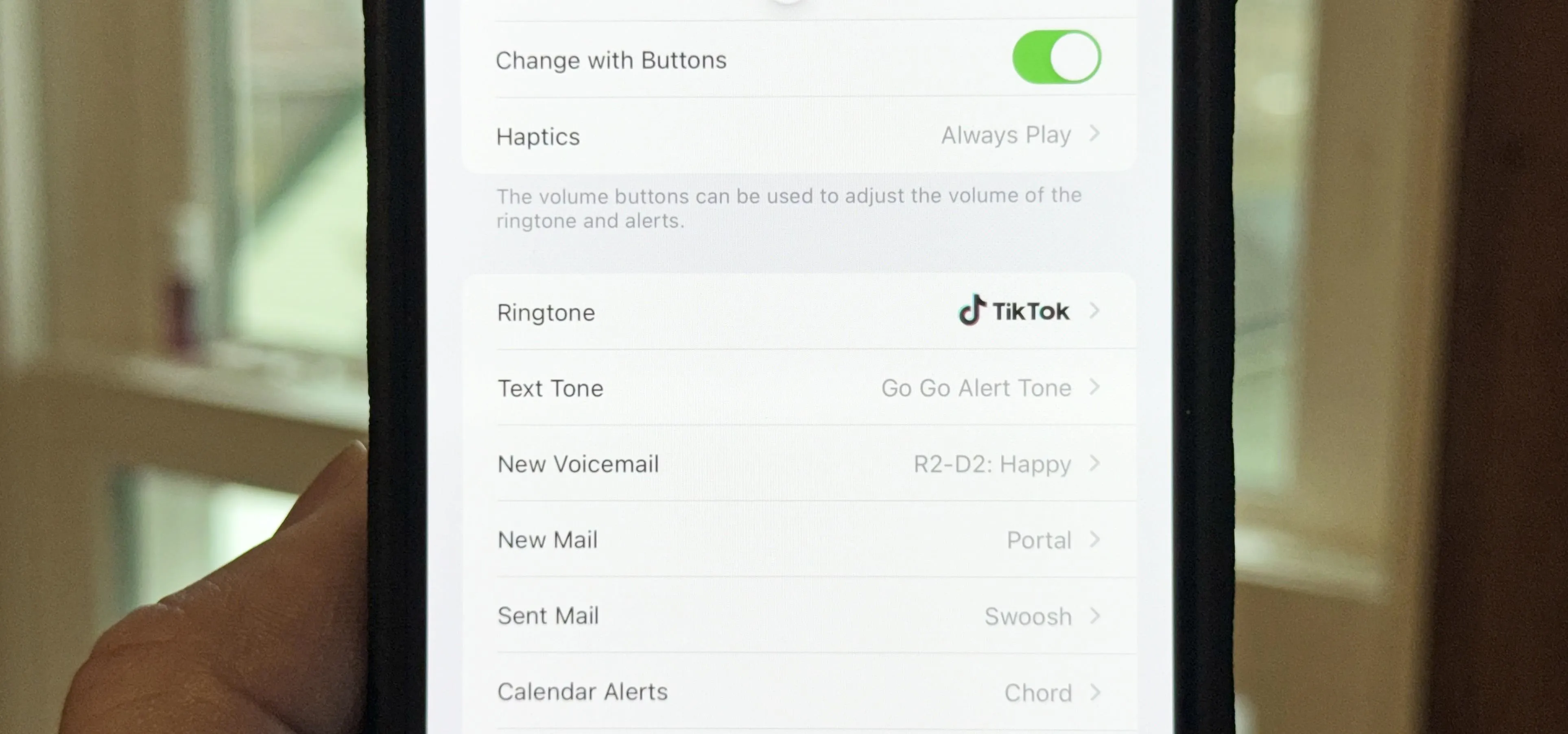
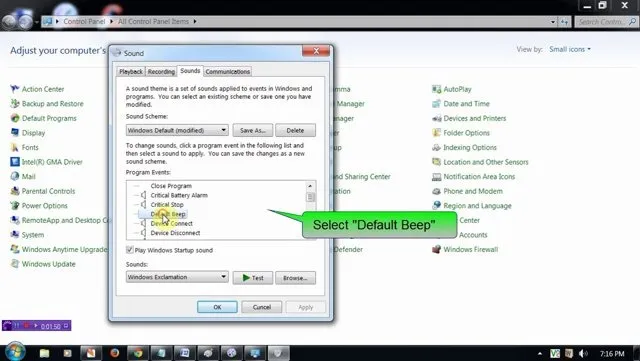
Music & Audio








Featured On WonderHowTo:
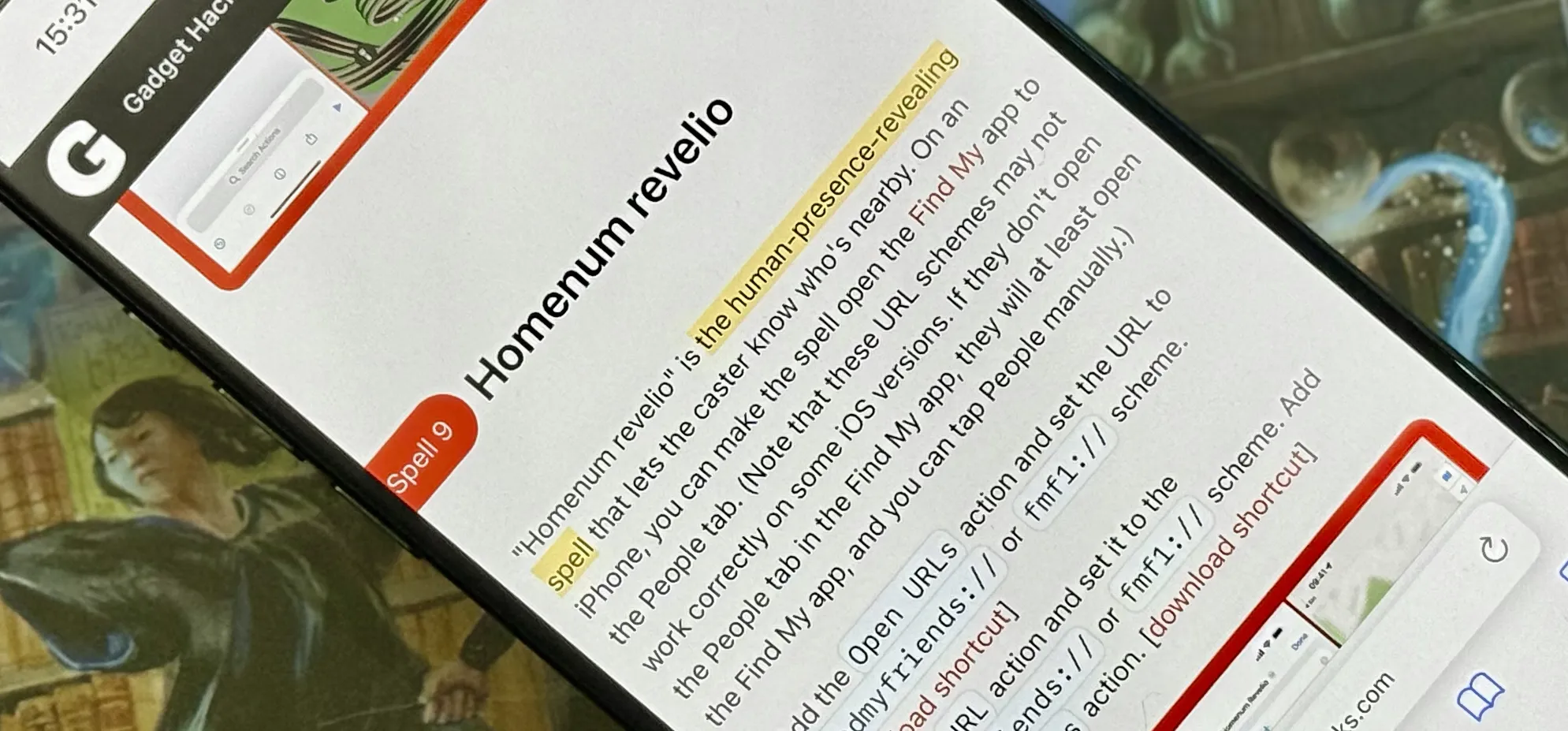
Augmented Reality







Featured On WonderHowTo:
Gaming